Syndicated here from a post on the CDW Research Hub published on March 21, 2024.
Allowing third parties access to organizational systems means striking a careful balance between enabling collaboration while safeguarding sensitive data and company credentials. To achieve this balance, effective lifecycle management is essential.
While it may have not been the case five years ago, the simple fact is that most organizations today work closely with third parties to reduce costs or supplement organizational abilities.
Especially since the boom of remote work, third-party access to organizational systems and networks has become an inevitability. But with credential theft being one of the leading causes of breaches, how do you promote necessary collaboration with external parties while safeguarding sensitive data and critical systems?
Common Challenges of Third-Party Access Management
For most organizations, collaboration with third-party vendors, contractors and partners isn’t a luxury, it’s a necessity. However, since many third parties will require access to internal systems and sensitive data, this collaboration introduces a number of risks.
The challenge lies in balancing the need for efficient collaboration with appropriate governance in place to manage access. What are the risks of not effectively managing this access?
Consider the results of this survey from several years ago, where 56 percent of full-time company employees surveyed reported that they would be willing to sell their credentials for just $150.
Despite the fact that most employees have some sense of ownership in the companies they work for and feel a sense of belonging, more than half reported that they would be willing to sell their corporate credentials for a meager payout. Since this survey was conducted, remote work has boomed, and mergers and acquisitions have led to an expanded, global workforce with a greatly expanded third-party worker presence.
The current landscape has dramatically heightened this type of insider threat, a risk to an organization that originates from inside the company. So, the question becomes: What would it take for a third-party or contingent worker with no sense of permanent belonging to a company to consider selling their credentials?
The unfortunate truth is that the larger the landscape, the greater the insider threat risk becomes.
A Lifecycle Approach to Third-Party Access
How many third-party users currently have access to your systems and networks? How many will have access 90 days from now? If you know the answer to this question offhand, you’re probably in the minority of organizations.
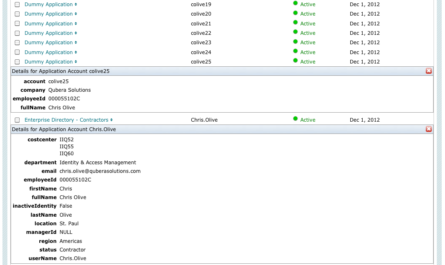
Most organizations have a single source of truth to ensure trust among their employees: a human resources (HR) department. HR will verify the identities and backgrounds of all full-time workers before the organization even decides let them in the building. Once vetted and hired, the IT department will allow them uninterrupted access to the systems, data and applications they need to do their jobs.
When a third-party or contingent worker comes on board, however, this same HR system of vetting and verifying the identities of individuals no longer applies. How can you be sure that third-party workers are able to access the data and systems they need during the time they’re contracted to work, but also ensure that access is removed when they’re no longer working for the company?
While manually managing hundreds of third-party users is possible, manually managing lifecycle access — the timeline from onboarding to offboarding a third party on your networks and systems — takes careful verification, management and governance.
Using the paradigm of least privilege access, the lifecycle approach takes into account every type of access that users need to access systems, applications and data while emphasizing the importance of:
- Thorough identity verification
- Access provisioning based on defined roles and permissions
- Ongoing monitoring for anomalous activities
- Timely offboarding to mitigate risks upon termination of engagement
Best Practices for Lifecycle Management
Lifecycle management essentially works like this: once a third-party user is approved to do work for an organization for a set amount of time, their identity and systems are verified, limited access is granted to organizational systems, and once the third-party worker’s contract has expired, access to those systems is revoked.
For an organization managing a few third-party users, this may not be a challenge; however, for an organization managing hundreds or thousands of users, it’s a herculean task.
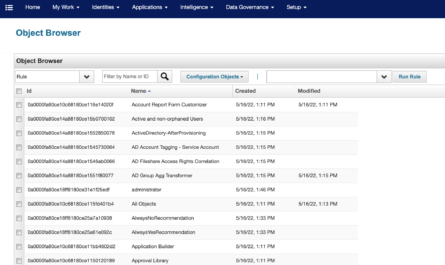
A single source of truth — a centrally managed repository or tracking system — is essential to managing lifecycle access to third parties. A modern Identity Governance and Administration (IGA) or modern identity and access management (IAM) platform will provide centralized control over user identities and access policies, enabling automation of access workflows and integration with advanced threat detection mechanisms.
Adhering to a few key best practices within IAM will ensure that third parties have secure access to the systems and data they need when they need it, and then revoke that access when no longer needed. These best practices include:
- Establish clear access policies. Understand which users need access to specific systems and ensure that those users are only approved to access those systems.
- Implement multi-factor authentication. Be sure that the users accessing your networks and data are who they say they are.
- Conduct regular reviews of access permissions. After a third-party user’s term has ended, all access should be terminated. If their term is extended, review whether that access should be extended.
- Encrypt sensitive data through network segmentation and application segmentation.
- Provide security awareness training to be sure that third-party users understand the risks of common cyberattacks (such as social engineering) as well as your full-time workers do.
Upholding Trust in a Risky Digital Landscape
Whether you manage a few select third-party users or a thousand, the interconnected nature of business and technology today indicates that you’ll likely be managing more users tomorrow. When the time comes to scale up, wading through the chaos of lifecycle management for thousands of users can be overwhelming. And yet, failure to do so can potentially compromise data integrity and trust or, worse, allow insider threats into your critical systems, applications and data.
Engaging an expert partner with deep expertise in both IAM and cybersecurity can help in an advisory capacity to design a system that accommodates your current business needs and allows you to scale as needed, adding capabilities for vendor lifecycle management, capacity to identity-proof incoming workflows, and more. Even better, IAM experts can help standardize processes and workflows to automate the entire process.